Zero Trust Networking: Beyond the Perimeter
Zero Trust Networking: Beyond the Perimeter
For decades, enterprise security relied on the Castle-and-Moat model. You built a strong firewall (the wall) and a VPN (the moat). If you were inside the IP range, you were "Trusted." If you were outside, you were "Suspicious."
In 2026, this model is dangerously obsolete. Cloud-native architectures, SaaS integrations, and the API economy have dissolved the perimeter. This 1,500+ word guide investigates the Science of Zero Trust. We will explore why "IP Addresses" are no longer relevant for security and how to build an identity-centric network that protects your data even when your infrastructure is compromised.
1. Hardware-Mirror: The Physics of the mTLS Handshake
Zero Trust relies on Mutual TLS (mTLS) for every connection.
The Problem: The Cryptographic Tax
Encrypting a packet is not free. It involves complex math (typically Elliptic Curve Cryptography) that consumes CPU cycles.
- The Physics: A standard TLS handshake requires multiple round-trips. If Service A talks to Service B, they must exchange "Passports" (Certificates) and agree on a key.
- The Hardware Reality: On a high-traffic host, mTLS can consume 5%-15% of total CPU power.
- The Architectural Solution: Senior architects use Crypto-Offloading. By using specialized hardware like AWS Nitro chips or Google Titan, the cryptographic work is moved away from the main CPU, ensuring that your security layer doesn't create "Tail Latency" for your users.
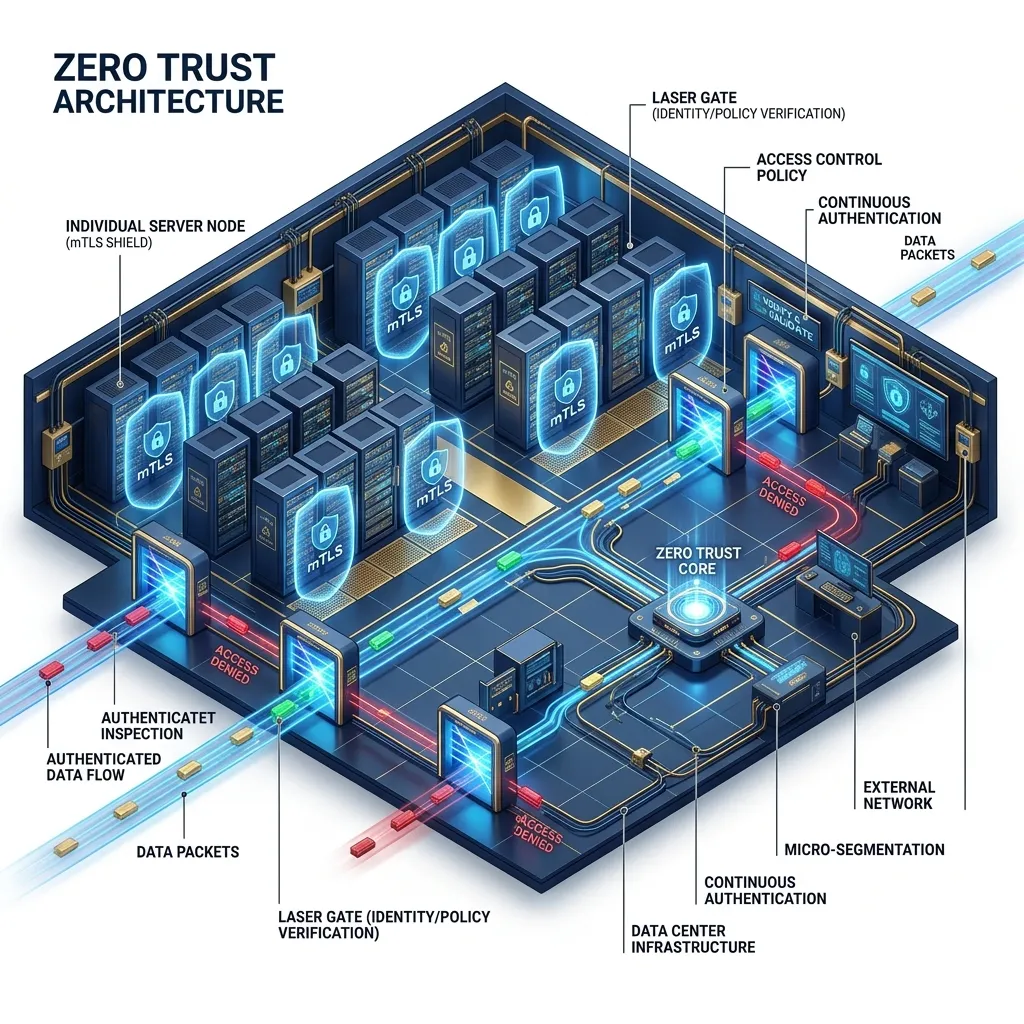
2. Assumed Breach: The Lateral Movement Neutralization
The primary goal of Zero Trust is to reduce the Blast Radius.
- The Old World: If a hacker compromised a single printer, they were "On the network" and could reach the main Database.
- The Zero Trust World: Every service lives in its own "Micro-perimeter."
- The Logic: The
BillingServicehas no "Trust" in thePrintingService. For the printer to talk to the database, it must provide a valid Workload Identity (Review Module 64). Without it, the network itself (not the app code) drops the packet.
3. SPIFFE and SPIRE: Giving the Hardware an Identity
How do you identify a "Process" in a world where containers live for seconds?
- SPIFFE (Secure Production Identity Framework For Everyone).
- The Architecture: Every workload is given a unique SVID (a certificate). This SVID contains no IP data; it only describes "Who" the service is (e.g.,
spiffe://prod/app/payment-gateway). - The Implementation (SPIRE): An agent runs on the hardware and performs Workload Attestation. It looks at the binary's process ID, its checksum, and its parent process to "Prove" it is the real app before handing it a certificate. This prevents "Impersonation Attacks" at the OS level.
4. The Control Plane vs. The Data Plane
A Zero Trust network is split into two logical layers.
The Data Plane (The Traffic)
This consists of proxies (like Envoy or Linkerd) that sit in front of every service. Every bit of data flows through these proxies.
- Function: They handle mTLS, encryption, and telemetry.
The Control Plane (The Brain)
This is the central authority (like Istio or Cloudflare) that manages the "Allow List."
- Function: It tells the proxies: "The PaymentService is allowed to talk to the DB, but only on Port 5432 using a POST request."
- The Scaling Logic: The Control Plane can update $10,000$ proxies in seconds, allowing you to "Kill" a hacked service's identity across the entire global network instantly.
5. Defense: Beyond the Identity (Context-Aware Access)
Identity is only 50% of the story. You also need Context.
- The Strategy: Use a Policy Engine (like Open Policy Agent - OPA).
- The Check: A request arrives with valid credentials. But the request is coming from a device that hasn't been updated in 200 days and from an IP address that was recently flagged for DDoS attacks.
- The Result: Zero Trust says DENY. Security is no longer a static "Yes/No"; it is a real-time calculation of Risk.
6. Summary: The Zero Trust Architect's Checklist
- Identity Over IP: Stop using IP addresses in your firewall rules. Use Workload Identifiers.
- Mutual Authentication: Every service must verify the identity of the caller AND the receiver.
- Hardware-Offload Check: Monitor your host CPU usage. If mTLS is causing lag, move to hardware-accelerated instances (Nitro/Titan).
- Least Privilege: Start with "Deny All." Only add "Allow" rules for the specific API routes required for the business logic.
- Encrypt Everything: In 2026, even "Internal" traffic is treated as "Public" traffic. Never send unencrypted data across the rack.
Zero Trust is the ultimate architectural response to the complexity of the global threat landscape. By assuming the network is hostile and verifying identity at every step, you build a system that is resilient to compromise. You move from a "Castle" model to a "Biological Immune System" where every service protects itself.
Phase 63: Implementation Actions
- Audit your current internal network: Can the "Service A" talk to "Service B" without a password? If yes, you have a security debt.
- Implement a Service Mesh (Istio/Linkerd) in a staging cluster to test mTLS overhead.
- Research eBPF (Cilium) for identity-based security at the kernel level.
Read next: Compliance as Code: Automating Regulatory Architecture ->
Part of the Software Architecture Hub - securing the edge.
