Compliance as Code: HIPAA & PCI-DSS Architectures
Compliance as Code: HIPAA & PCI-DSS Architectures
For many architects, "Compliance" (HIPAA for health data, PCI-DSS for payments) feels like a manual checklist handled by lawyers and paper-pushers. It is often seen as a "Blocker" to engineering speed.
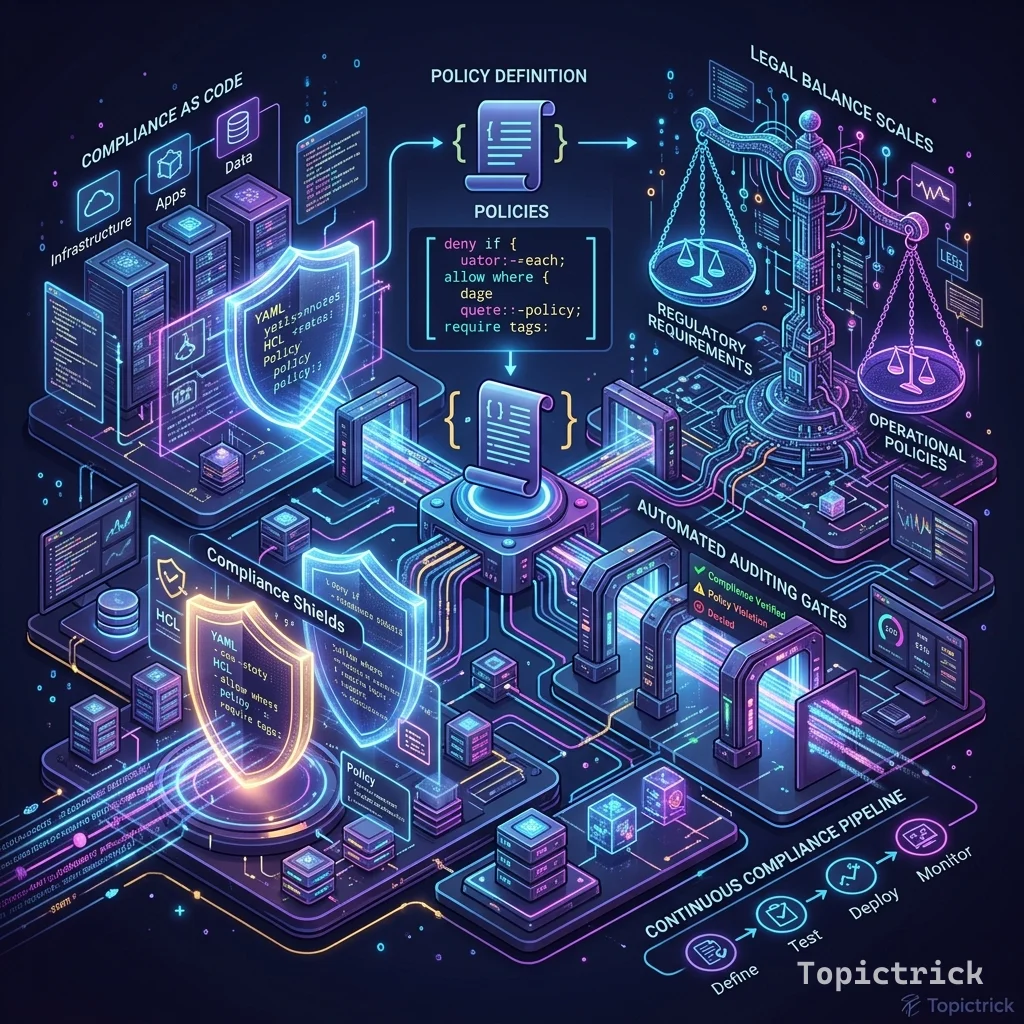
In 2026, the elite companies-those that handle billions in clinical trials or financial trades-treat Compliance as a First-Class Software Property. This 1,500+ word guide investigates the Science of Automated Compliance. We will explore how to embed regulatory constraints directly into your CI/CD pipelines, making the actual audit a non-event.
1. Hardware-Mirror: The Physicality of Data Sovereignty
Regulatory compliance is not abstract; it is tethered to Physical Silicon.
HSM (Hardware Security Modules) & KMS
HIPAA and PCI-DSS both mandate that encryption keys be strictly isolated.
- The Physics: If a hacker gain root access to your application server, they should not be able to find the encryption key in the server's RAM.
- The Hardware Solution: You must use Hardware Security Modules (HSM). These are dedicated, tamper-proof chips (like AWS CloudHSM or physical chips in a data center) that perform the math of encryption.
- The Protocol: The key never leaves the HSM. The server sends the data to the HSM, the HSM encrypts it and sends the ciphertext back. If you lose control of the server, the keys remain physically unreachable.
3. The Immutable Audit Trail: WORM Storage Physics
A log that can be deleted is not an audit; it is a suggestion. In high-compliance environments, you must use WORM (Write Once, Read Many) storage.
S3 Object Lock & Compliance Mode
- The Physicality: When you enable "Compliance Mode" on an S3 bucket with Object Lock, the cloud provider's underlying storage layer (the bits on the disk) are physically prevented from being overwritten or deleted.
- The "Safety Key": Not even the account's "Root" user or the cloud provider's support team can delete the data until the retention period (e.g., 7 years) expires.
- The Architect's Pivot: You must architect your logging pipeline such that ALL application logs (Review Module 59) are "Tee'd" into this immutable bucket. This provides an indestructible chain of evidence that can survive even a full account compromise.
4. Continuous Drift Detection: The 24/7 Virtual Auditor
Compliance is often lost in the "Middle of the Night" when an engineer manually opens a port to fix a production fire.
The Problem: Configuration Drift
An architect defines a secure VPC. A month later, after 100 manual changes, the VPC is a sieve.
- The Solution: Cloud Custodian or AWS Config.
- The Logic: These tools perform a "Scan" every few minutes. They compare the Live State of the hardware against the Desired State defined in your Policy-as-Code.
- Auto-Remediation: If a bucket is found to be "Public" in a PCI-scoped account, the system doesn't just "Alert"-it physically closes the bucket within 60 seconds of the violation. This is the move from "Passive Auditing" to "Active Enforcement."
5. The Policy Engine: Rego & OPA Internals
To implement Compliance as Code, you need a "Judge" that lives in your CI/CD pipeline.
Why Rego?
Rego (the language for Open Policy Agent) is a Declarative language. You don't tell the system "HOW" to check a bucket; you describe "WHAT" a compliant bucket looks like.
- The Filter Storm: In a large cluster, OPA can evaluate thousands of requests per second with sub-millisecond latency.
- The Architecture: OPA is often deployed as a "Sidecar" (Review Module 69). This ensures that authorization decisions are made Locally on the node, avoiding the "Network Hop" to a central authorization server.
6. Architecting for HIPAA and PCI-DSS in 2026
Modern compliance is about Logical Isolation rather than physical walls.
HIPAA (The Clinical Shield)
HIPAA is about the Integrity and Privacy of health data (PHI).
- The Key: HSM Isolation. Use Hardware Security Modules to ensure that PHI encryption keys are never visible to the application memory.
- The Audit: Use ABAC (Attribute-Based Access Control) to prove that only the "Assigned Doctor" physically accessed a specific row in the database.
PCI-DSS: The CDE VPC
If you are a bank, you must build a Cardholder Data Environment (CDE).
- The Design: A separate, air-gapped VPC. Only the "Payment Service" can talk to the "Card Vault." All traffic is logged and decrypted by a dedicated security proxy.
- The Lever: Use Tokenization to move your core backend "Out of Scope." If your server never sees a credit card number, you don't have to audit it.
4. Automation: The Policy Engine (OPA & Rego)
To implement Compliance as Code, you need a "Judge" that lives in your CI/CD pipeline.
- The Tool: Open Policy Agent (OPA).
- The Language: Rego.
- The Workflow: When a developer submits a PR, the OPA engine reads the Terraform Plan.
- The Rule:
deny[msg] { input.resource_type == "aws_s3_bucket"; not input.encryption_enabled; msg = "Bucket not encrypted. PCI Violation." }. - The Result: The build fails. The developer is corrected by the "Machine," not a "Lawyer."
5. Drift Detection: The 24/7 Auditor
Compliance isn't just about the "Deploy Day"; it's about the "Middle of the Night."
- The Problem: Configuration Drift. An engineer manually opens a port on a firewall to fix a bug.
- The Solution: Cloud Custodian or AWS Config.
- The Logic: These tools perform a Hardware Audit every 10 minutes. If they find a non-compliant firewall rule, they don't just "Alert"; they Automatically Remediate (close the port).
6. Summary: The Compliance Architect's Checklist
- Identity-Based Logging: Don't log "User logged in." Log "Identity X using Certificate Y performed Action Z on Row A."
- Immutable Logs: Ensure all compliance logs are stored on WORM storage with cryptographic hashing to prove they haven't been tampered with.
- HSM Key Separation: Separate your KMS (Key Management Service) from your compute layer physically.
- Policy-Fail-Fast: Implement OPA checks in your local
git commithooks so developers find violations before they even push. - Evidence Collection: Build an automated "Evidence Lake." Instead of manually taking screenshots for auditors, your IDP (Review Module 57) should automatically export infrastructure state every 24 hours.
Compliance is not the enemy of speed; Manual Compliance is. By codifying your regulatory requirements into the silicon and the pipeline, you provide the "Guardrails" that allow your engineering team to move at a "Breakneck Pace" with 100% legal safety. You graduate from "Managing paper" to "Architecting Integrity."
Phase 64: Compliance Actions
- Evaluate your current "Time to Audit." If it takes more than 1 week, you need to automate your evidence collection.
- Implement an OPA check for your core infrastructure repository.
- Enable S3 Object Lock on your primary audit logging bucket.
- Review your HSM Strategy: Ensure your primary encryption keys are stored in a hardware module, not an application secret file.
Read next: Advanced Caching Strategies: Architecture for Global Scale ->
Part of the Software Architecture Hub - trust through code.
