CICS Architecture: Regions, Tasks, DSA & Address Spaces on z/OS
CICS Architecture: A Complete Technical Guide
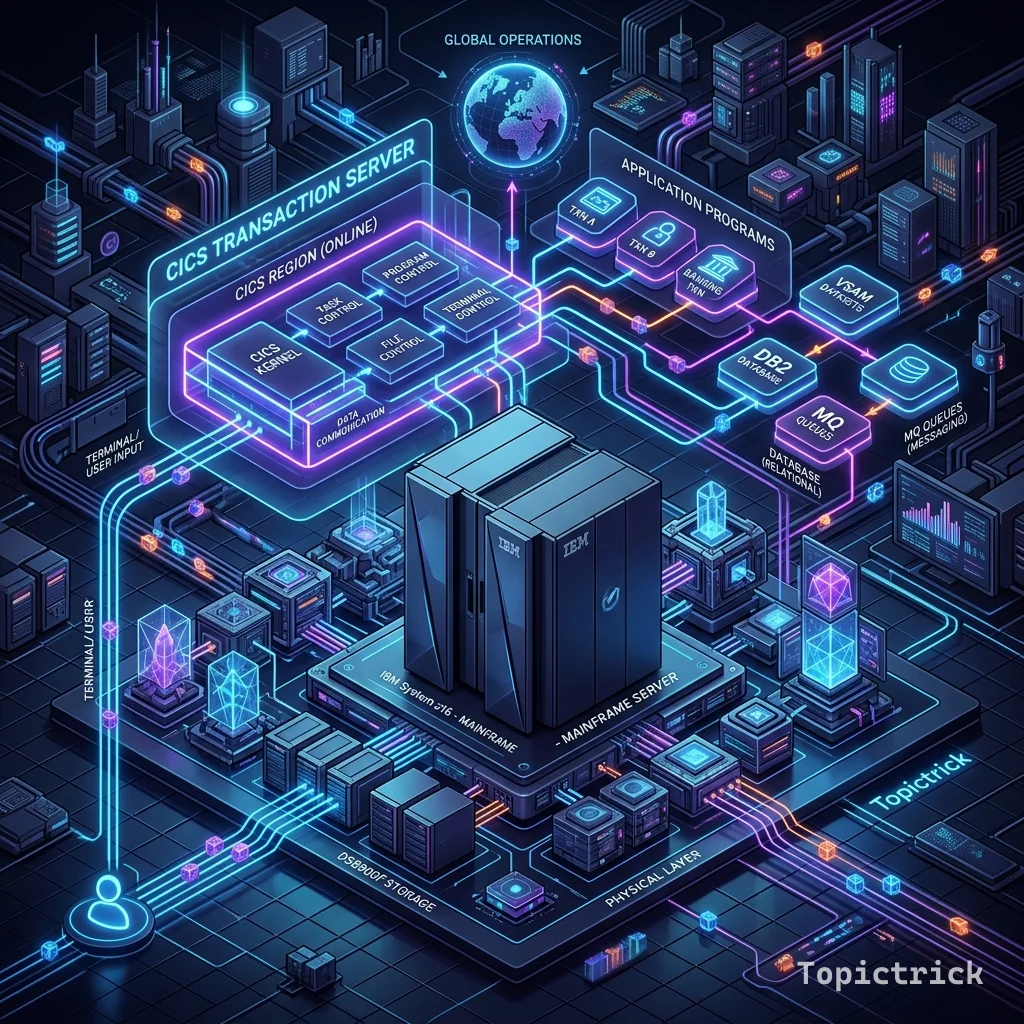
Before writing a single line of CICS code, understanding the architecture of a CICS region pays dividends for years. The architectural decisions IBM made — multi-tasking within a single address space, cooperative scheduling, transaction-based resource management — are the reason CICS can process millions of transactions per second with five-nines reliability. They also explain the design patterns (pseudo-conversational programming, COMMAREA-based state) that CICS developers follow.
The CICS Region
A CICS region is a running instance of CICS Transaction Server (CTS). On z/OS, it executes as one or more address spaces — protected memory regions managed by the operating system. A CICS region is:
- Independent of other regions — a problem in one region does not affect others
- Identified by its APPLID (1-8 characters, e.g., CICSPROD, CICSD01)
- Started as a z/OS started task (STC) from the JES initiator
- Configured by a System Initialization Table (SIT) and associated parameters
z/OS LPAR
├── CICS Region: CICSPROD (Production)
│ ├── Main address space (QR TCB + execution)
│ ├── Async Pool (CICS auxiliary threads)
│ └── Open TCP/IP Listener (DDF/Web)
├── CICS Region: CICSD01 (Development)
└── CICS Region: CICST01 (Test)In large organisations, production may consist of a CICS CICSplex — a cluster of related regions managed together, with workload routed between them by CICS Workload Manager (CWM).
CICS Address Space Structure
A CICS region runs primarily in one z/OS address space called the QR (Quasi-Reentrant) address space. This single address space contains:
- The CICS nucleus (kernel code)
- All concurrently executing user programs
- All data for all active tasks
- CICS system tables and resource definitions
This is the key architectural insight: unlike a Unix process model where each connection gets its own process or thread, CICS runs thousands of tasks concurrently within a single address space, managed by CICS's own internal scheduler (the dispatcher).
Modern CICS also uses additional address spaces:
Auxiliary address spaces: For Java (Liberty JVM), FEPI (Front End Programming Interface), and some pipeline processing. These run outside the QR address space.
Open TCP/IP listener: A separate z/OS address space for the CICS Web Support, handling HTTP connections before passing requests into the CICS region.
The CICS Dispatcher
The dispatcher is the heart of CICS multitasking. It is responsible for deciding which task runs next and for how long.
CICS uses a cooperative multitasking model (not preemptive). A task runs on a TCB (Task Control Block — a z/OS thread) until it voluntarily gives up control by making a CICS service call:
Task A starts → issues EXEC CICS READ (file I/O started) → suspended
→ Dispatcher gives CPU to Task B
Task B runs → issues EXEC CICS SEND MAP (terminal I/O) → suspended
→ Dispatcher gives CPU to Task C
...
Task A's file I/O completes → Task A made ready → Dispatcher resumes Task AThis model is extremely efficient — there is no preemption overhead, and context switches occur at natural wait points (I/O, lock waits) rather than at arbitrary time slices.
Dispatch classes: CICS groups tasks into dispatch classes (terminal-initiated, internal, clock, etc.) and assigns priority within each class. High-priority work (CICS system tasks, real-time transactions) gets CPU before lower-priority work.
Multiple TCBs (QR + Open TCBs): Modern CICS runs user programs under multiple TCBs:
- QR TCB: Traditional COBOL programs run quasi-reentrant under the QR TCB
- Open TCBs (L8, L9): Java and threadsafe COBOL/PL/I programs run under open TCBs for true parallelism
CICS Task Lifecycle
Every CICS transaction invocation creates a task. Here is the full lifecycle:
1. TASK ATTACH
↓ User presses ENTER or API request arrives
CICS identifies the transaction ID → looks up transaction definition
→ Validates authority → Creates a task control block (TCB)
→ Allocates storage (User Transaction Storage)
2. TASK DISPATCH
↓ Dispatcher allocates CPU
CICS loads the initial program → transfers control
3. PROGRAM EXECUTION
↓ Program issues EXEC CICS commands
Each command → CICS kernel processes it
→ Program may call other programs via LINK/XCTL
→ Program issues EXEC CICS RETURN when done
4. TASK DETACH
↓ EXEC CICS RETURN with no TRANSID
CICS frees all task storage
→ Releases all file locks held by the task
→ Commits or rolls back resource manager changes (SYNCPOINT)
→ Releases the TCB for reuseCICS Storage Architecture
Memory management in CICS is the responsibility of the CICS Storage Manager. All storage within the CICS region is drawn from the Dynamic Storage Area (DSA).
DSA Sub-areas
Below 16MB line (31-bit addressing limit — legacy):
├── CDSA (CICS DSA) — CICS system storage
└── UDSA (User DSA) — User program storage (legacy programs)
Above 16MB line (extended addressing):
├── ECDSA (Extended CDSA) — CICS system storage
├── EUDSA (Extended UDSA) — User program storage (modern programs)
└── ERDSA (Extended RDSA) — Read-only shared programs (reentrant code)
64-bit (MEMLIMIT):
└── GCDSA/GUDSA — Very large storage allocations (BLOBs, large data)Storage Types
Task-lifetime storage: Allocated when a task starts, freed when it ends. This is what GETMAIN USER provides — you do not need to explicitly free it; CICS does it at task end.
Shared storage: Allocated by one task and accessible by others (GETMAIN SHARED). Must be explicitly freed with FREEMAIN. Used for inter-task data sharing.
Program storage: Shared across all tasks using the same program (reentrant programs in ERDSA). This allows 1,000 concurrent tasks to share one copy of a program's executable code.
Storage Violations
A storage violation occurs when a task writes beyond its allocated storage into another task's storage or CICS system storage. CICS detects violations and typically abends the offending task. Common causes:
- Writing past the end of a WORKING-STORAGE area
- Incorrect pointer arithmetic
- Wrong GETMAIN/FREEMAIN pairs
Enable CICS storage protection (STGPROT=YES in SIT) in test environments to catch violations early.
CICS Resource Tables
CICS maintains in-memory tables of all its resource definitions — loaded at startup from the CSD (CICS System Definition) dataset:
Program Definitions (PROGRAM): Which programs can be called, their language (COBOL, PL/I, Assembler, Java), and storage attributes.
Transaction Definitions (TRANSACTION): Which program each transaction ID (TRAN) invokes, priority, timeout, security key, and DB2 attachment settings.
File Definitions (FILE): VSAM datasets accessible to CICS programs — VSAM cluster name, read/write/browse access, sharing options, and record format.
Terminal Definitions (TERMINAL): 3270 terminal sessions, their network addresses, and which typeterm definition governs them.
DB2 Entries (DB2ENTRY): How CICS connects to DB2 — thread pool size, plan name, authorization ID.
-CICSPROD CEMT INQUIRE PROGRAM(EMPINQ)
PROGRAM(EMPINQ) LENGTH(00004096) LANGUAGE(COBOL) STATUS(ENABLED)Resources can be enabled/disabled dynamically using the CEMT master terminal transaction without restarting the region.
CICS Transaction Server Versions
| Version | z/OS | Key Features |
|---|---|---|
| CICS TS 5.3 | z/OS 2.1+ | Java 8, cloud connectors |
| CICS TS 5.4 | z/OS 2.2+ | API-first, zEDC compression |
| CICS TS 5.5 | z/OS 2.3+ | gRPC, JSON web services |
| CICS TS 5.6 | z/OS 2.4+ | OpenTelemetry, GraphQL |
| CICS TS 6.1 | z/OS 2.5+ | Cloud native integration, AI toolkit |
Multi-Region Operation (MRO)
Most production CICS environments use multiple interconnected regions rather than one large region. The primary topology types:
Terminal-Owning Region (TOR): Owns all terminal connections. Receives all initial transaction requests. Routes them to the appropriate AOR.
Application-Owning Region (AOR): Runs application programs. Has no direct terminal connections — all I/O goes through the TOR.
File-Owning Region (FOR): Owns VSAM files. Multiple AORs can share files through the FOR, eliminating the need for VSAM shareoptions.
DB2-Owning or Batch-Support Region: Specialised regions for specific workloads.
3270 Terminal → TOR (Transaction Routing)
→ AOR1 (Application Execution)
→ AOR2 (Application Execution)
↕ Function Shipping
FOR (VSAM File Access)MRO connections use the Multi-Region Operation facility — high-speed internal communication between regions in the same Sysplex without going through TCP/IP.
CICS and Parallel Sysplex
In the largest mainframe installations, CICS runs in a Sysplex configuration — multiple z/OS LPARs sharing data and workload:
- CICSplex: A set of CICS regions managed as a single entity by CICSPlex System Manager (CPSM)
- Workload routing: Incoming transactions are routed to the least-loaded AOR automatically
- Shared queues: CICS Shared Temporary Storage uses Coupling Facility for TS queues visible to all regions
- XCF communication: Cross-system coupling facility enables locking and data sharing across LPARs
This architecture allows a bank to run 50+ CICS regions across 10+ LPARs, processing millions of transactions per second with automatic failover if any LPAR fails.
Next Steps
With the architecture clear, the next step is understanding how transactions and tasks flow through the CICS lifecycle. Read How CICS Transaction Processing Works for a step-by-step walkthrough. Then explore CICS Resource Definitions to understand the resource types you will work with every day. Follow the full learning path at the CICS Mastery course hub.
Frequently Asked Questions
Q: What are the main components of the CICS architecture? CICS consists of a Transaction Manager that schedules and dispatches tasks, a Storage Manager that controls dynamic memory, a File Control component for VSAM and non-VSAM data access, a Program Control component that loads and links programs, and a Terminal Control component that manages communication with terminals and networks. On z/OS, CICS runs as an address space (region) under the operating system and integrates tightly with z/OS services like SMF, RRS, and RACF.
Q: How does CICS differ from a regular batch processing environment? Batch runs programs sequentially to completion, often processing entire files in one job step. CICS is an online transaction processing (OLTP) environment where thousands of short, user-initiated transactions run concurrently, each completing in milliseconds. CICS manages multitasking within a single address space using non-preemptive dispatching, allowing far more transactions per second than spawning a new OS task for each.
Q: What is the CICS nucleus and what role does it play? The CICS nucleus is the core set of CICS modules loaded at region startup that provide fundamental services — storage management, task control, program management, and terminal I/O. All user programs run in the same address space as the nucleus and call it via the EXEC CICS command interface. The nucleus is always resident in memory and is the foundation on which all CICS services are built.
